NeuVector Adds Production-grade Protection to VMware Tanzu Kubernetes Platform
NeuVector’s mission is to provide enterprise-ready security to companies deploying modern container and Kubernetes infrastructures. Most companies understand the need to scan applications for vulnerabilities, but many are challenged to provide strong security for production applications. NeuVector delivers full lifecycle container security that addresses this issue and protects corporate assets. Now, NeuVector can provide this advanced level of security to VMware Tanzu users.
VMware Tanzu is a suite of products that allow its customers to Build, Run, and Manage Kubernetes controlled container-based applications. To achieve its goal of managing both infrastructure and container orchestration, Tanzu offers several key functions for application lifecycle management:
- Packages and delivers Kubernetes applications using Pivotal and Bitnami technologies.
- The container host environment using PhotonOS.
- Delivers Project Pacific which re-architects vSphere to manage applications across VM’s or cloud resources with Kubernetes as the control plane.
- Centralized management of Kubernetes clusters running cross infrastructure and public cloud via Tanzu Mission Control.
As the all-in-one application platform, Tanzu leverages multiple existing VMware technologies to enhance its platform security:
- Data and credential encryption, application patching, compliance automation, logging and access controls.
- PhotonOS as a hardened host image with secured container runtime. Enabled AppArmor, Seccomp.
- NSX for network micro-segmentation. HTTP traffic is secured in TCP routing.
- vCenter SSO for identity and access management.
These core components provide the foundational security layers that any serious Kubernetes production environment would need. However Tanzu users should not misconstrue foundational security as being flexible enough to provide risk-based security for a distributed workload. This is especially true for mission-critical applications that run in production. Experienced operators will view Kubernetes Security from different angles:
- Stack view of Kubernetes Security:
The foundational controls for securing any container running environment requires a hardened platform for host security, access control, L3 network segmentation, secrets management, data encryption and more. Tanzu and Red Hat OpenShift are both well regarded implementations for foundational controls.
Additionally, basic operational controls and system are critical. Examples of these controls might be Kubernetes API service, container engine, service discovery and network service mesh or serverless system modules all should be monitored and secured. Production grade vulnerability management and continuous compliance checks will keep these infrastructure modules in good shape.
The last and most difficult capability is to secure running applications. It is the only place or time that an application comes “face-to-face” with hackers. A strong & comprehensive network plus endpoint security solution is the way to go. The required advanced security features include behavior locking down, and layer 7 network inspections, and data loss prevention, and must block any malicious processes, detect runtime privilege escalation, capture hidden crypto-mining containers or processes, and prevent container hijacking.
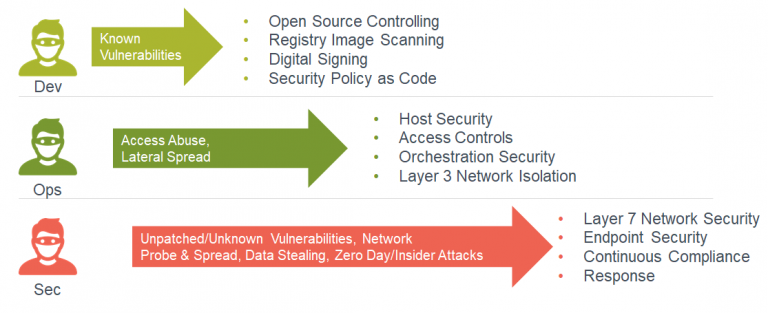
- DevSecOps: Security for Build-Ship-Run application pipeline:
Application containers are created through a modern automated pipeline. Security should be integrated and automated in same ways. Traditional security models slow down the pipeline because they require many manual operations, deployment and management. Gartner also published several reports that emphasized the importance of putting security in place for all 11 threat vectors in the application lifecycle pipeline.
NeuVector is the first Kubernetes-native solution in the market. We are focusing on Kubernetes container workload protection. NeuVector covers security throughout the container lifecycle, including the most comprehensive DevSecOps security automation capabilities. For example, we cover: security policy as code, CI/CD integration, policy-driven admission control, continuous compliance for running Kubernetes and its platforms and much more.

Thanks to VMware Tanzu for evolving to support Kubernetes natively in vSphere 7 core, which makes it straightforward and easy for the Kubernetes native eco-system vendors like NeuVector to be able to fit in and provide values for customers.

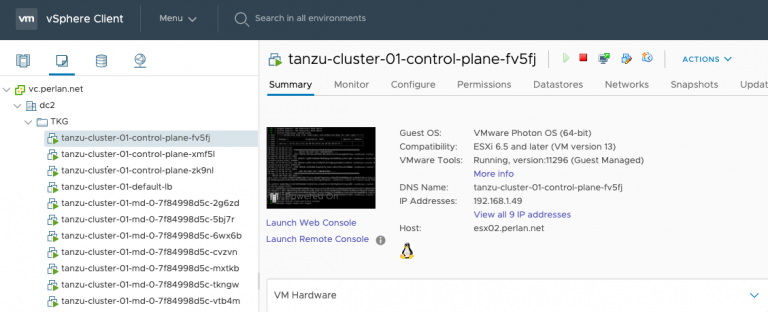
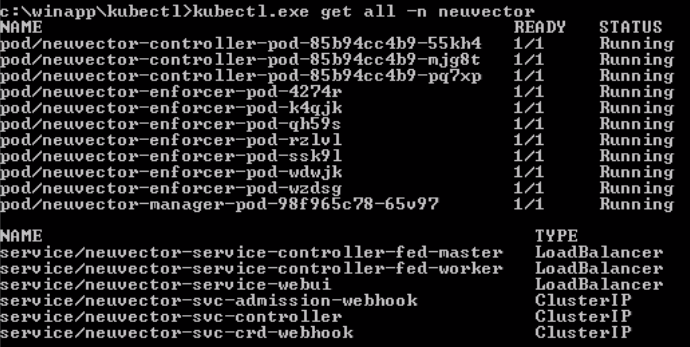
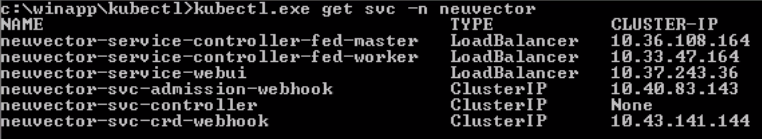
For customers, this is a simple way to deploy production-grade security without hassles. Recently, a NeuVector customer deployed NeuVector on top of Tanzu in 30 minutes without any issues:

Kubernetes native deployment is preferred:
Right after the deployment, the customer saw the results of the Tanzu PhotonOS scan by NeuVector and unsurprisingly, vulnerabilities were identified. The reality is that every day non-fixable vulnerabilities, out-of-date libraries or zero-day issues are pushed into production, which is why enterprises need strong runtime “virtual patch” protection, like that from NeuVector, to guard platforms.
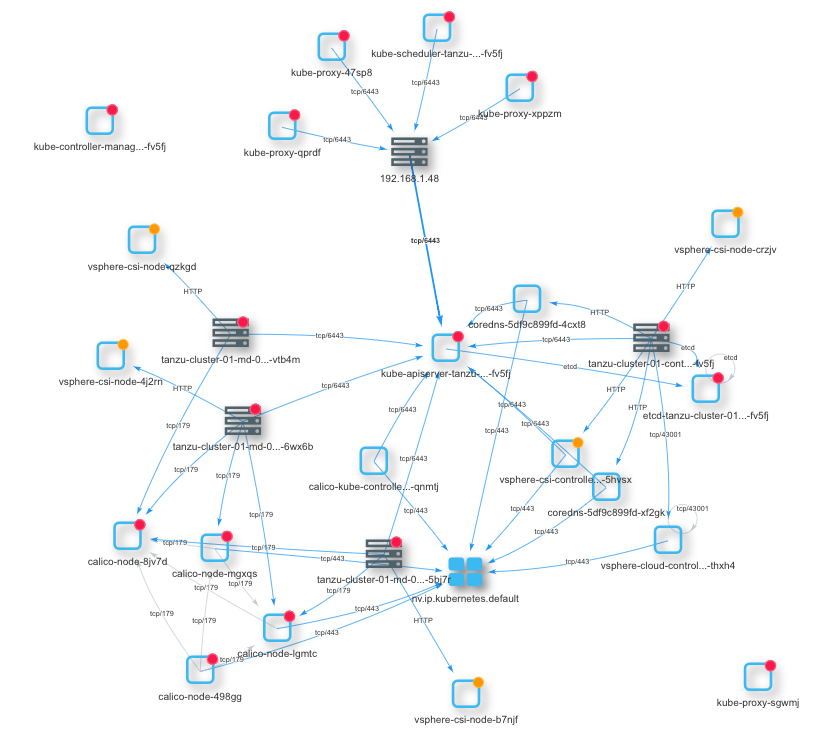
Some of the Tanzu system pods are monitored by NeuVector:
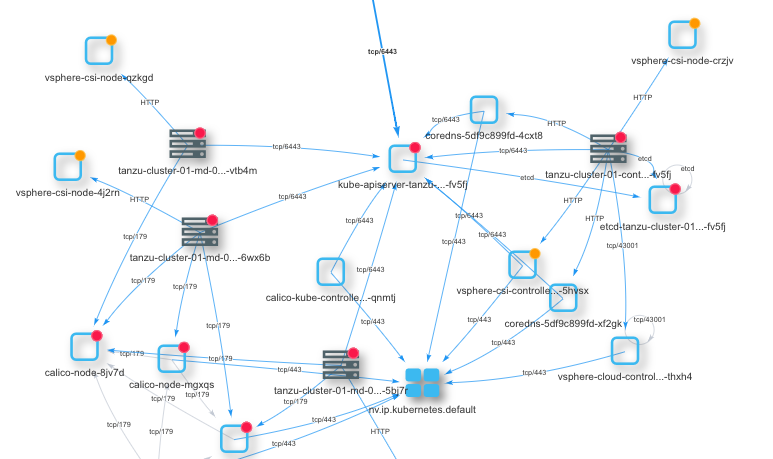
NeuVector services are running in Tanzu as an HA-enabled cluster that are automatically protecting all live pods including Tanzu system containers and its services.
As Kubernetes platforms grew, multi-cluster, multi-cloud application management became more and more realistic. Solutions like VMware Tanzu and Google Anthos are designed to manage cloud workloads at scale for modern Kubernetes environments. Security solutions like NeuVector are also empowered by Kubernetes. Wherever applications are running: hybrid cloud or multiple clouds or private cloud, platforms like Tanzu are designed to manage Kubernetes clusters to “free the apps”. NeuVector’s Kubernetes-native solution will enable enterprises to seamlessly add security to Tanzu platforms to “free the security.”
Related Articles
Feb 01st, 2023
Container Security: Network Visibility
Feb 01st, 2023
DevOps Transformation
Oct 25th, 2023